SSL: Who Do You Trust?
September 25, 2011 1 Comment
Note: This is a post that appeared on the site lbdigest.com about a year or so ago, but given that SSL is back in the news lately, I figured it’s worth updating and re-posting. Also, it features the greatest SSL diagram ever created. Seriously, if you fire up Visio/Omnigraffle, know the best you can hope for is second place.
One of the most important technologies used on Internet is the TLS/SSL protocol (typically called just SSL, but that’s a whole different article). The two benefits that TLS/SSL gives us are privacy and trust.
Privacy comes through the use of digital encryption (RSA, AES, etc.) to keep your various Internet interactions, such as credit card numbers, emails, passwords, saucy instant messages, confidential documents, etc., safe from prying eyes. That part is pretty well understood by most in the IT industry.
But having private communications with another party is all for naught if you’re talking to the wrong party. You also need trust. Trust that someone is who they say they are. For Internet commerce to work on a practical level, you need to able to trust that when you’re typing your username and password into your bank’s website, that you’re actually connecting to a bank, and not someone pretending to be your bank.
Trust is accomplished through the use of SSL certificates, CAs (certificate authorities), intermediate certificates, and certificate chains which combined is known as PKI (Public Key Infrastructure). To elaborate on the use of these technologies to provide trust, I’m going to forgo the traditional Bob and Alice encryption examples, and go for something a little closer to your heart. I’m going to drop some Star Trek on you.
Let’s say you’re in the market for a starship. You’re looking for a sporty model with warp drive, heated seats, and most importantly, a holodeck. You go to your local Starfleet dealer, and you find this guy.
Ensign Tony.
Seriously Tony, have you even talked to a girl?
The problem is, you don’t trust this guy. It’s nothing personal, but you just don’t know him. He says he’s Ensign Tony, but you have no idea if it’s really him or not. But there is one Starfleet officer you do know and trust implicitly, even though you never met him. You trust Captain Jean-Luc Picard.
Picard’s Law: Set up a peace conference first, ask questions later
Captain Picard is the kind of guy you start out automatically trusting. His reputation precedes him. Your browser is the same way, in that right out of the gate there are several sources (such as Verisign) that your browser trusts implicitly.
If you want to check out who your browser trusts, you can typically find it somewhere in the preferences section. For example, in Google Chrome, go into Preferences, and then Under the Hood. On a Mac this opens up the system-wide keystore for all the trusted certificates and keys. In other operating systems and/or browsers, you may have different certificate stores for different browsers, or like with a Mac all the programs may share a single centralized certificate store.
Back to the Star Trek analogy.
But you’re not dealing with Picard directly. Instead, you’re dealing with Ensign Tony. So Picard vouches for Ensign Tony, and thus a trust chain is built. You trust Picard, and Picard trusts Ensign Tony, so by the transitive property, you can now trust Ensign Tony.
That is the essence of trust in SSL.
Intermediate Certificates
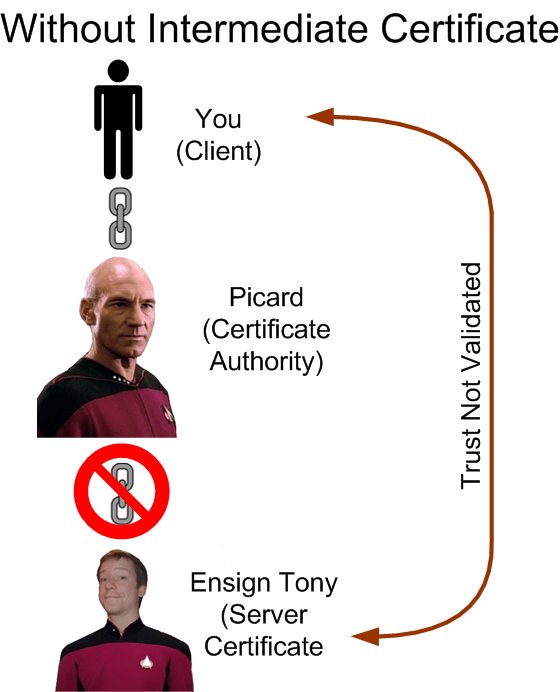
One of the lesser understood concepts in the us of SSL certificates is the intermediate certificates. These are certificates that sit between the CA (Picard) and the site certificate (Ensign Tony).
You see, Picard is an important man. The Enterprise has over a thousand crew members and he can’t possibly personally know and trust all of them. (In Ensign Tony’s case, there’s also the little matter of a restraining order.) So he farms the trust out to his subordinates. And one crew member he does implicitly trust is Chief Engineer Geordi La Forge.
Ensign Tony works for Geordi, and Geordi trusts Ensign Tony. Thus Geordi becomes the intermediate certificate in this chain of trust. You can’t trust Ensign Tony directly through Picard because Picard can’t vouch for Tony, but Geordi can vouch fro Tony, and Picard can vouch for Geordi, so we have built a chain of trust. This is why load balancers and web servers often require you to install an intermediate certificate.
This is the greatest SSL diagram ever made.
Here’s what happens when you don’t install an intermediate certificate onto your load balancer/ADC/web server:
You’re 34 years old Tony, you’d think you would have made Lieutenant by now
One of the practical issues that comes up with intermediate certificates is which one do you use? The various SSL certificate vendors such as Thawte, Digicert, and Verisign have several intermediate certificates depending on the type of certificate you purchase. Sometimes it’s not always obvious. If you have any doubts, use one of the SSL certificate validation tools from the various vendors , including this one by Digicert. It will tell you if the certificate chain works or not. Do not let a test from your browser determine whether your certificate works. Browsers handle certs differently, and a validation tool will tell you if it will work with all browsers.



Pingback: Creating Your Own SSL Certificate Authority (and Dumping Self Signed Certs) | The Data Center Overlords